For many organizations, legacy system integration has become an operational necessity. The reason is the fact that established platforms struggle to support cloud adoption, automation, and data processing needs. Yet, without disciplined software engineering, integration can simply extend technical debt instead of reducing it. A deliberate and planned system integration approach, guided by tech consulting, ensures structured, secure, and scalable integrations, enabling enterprises to introduce new capabilities, protect business continuity, reduce operational risk, control cost, and create a practical path toward gradual modernization.
We'll cover what legacy system integration entails, its distinction from modernization, organizational challenges, and legacy system integration strategies for lasting success.
What is legacy system integration?
Legacy system integration connects established, often business-critical systems with newer applications, platforms, or data environments so data flows uninterrupted. Rather than forcing immediate system replacement, integration enables organizations to extend the value of these assets while introducing modern capabilities such as cloud services, automation, analytics, and APIs. What does this mean in practice? Existing infrastructure continues to support daily operations, while new digital initiatives can access the same data and workflows without disruption.
What good integration can do for your system
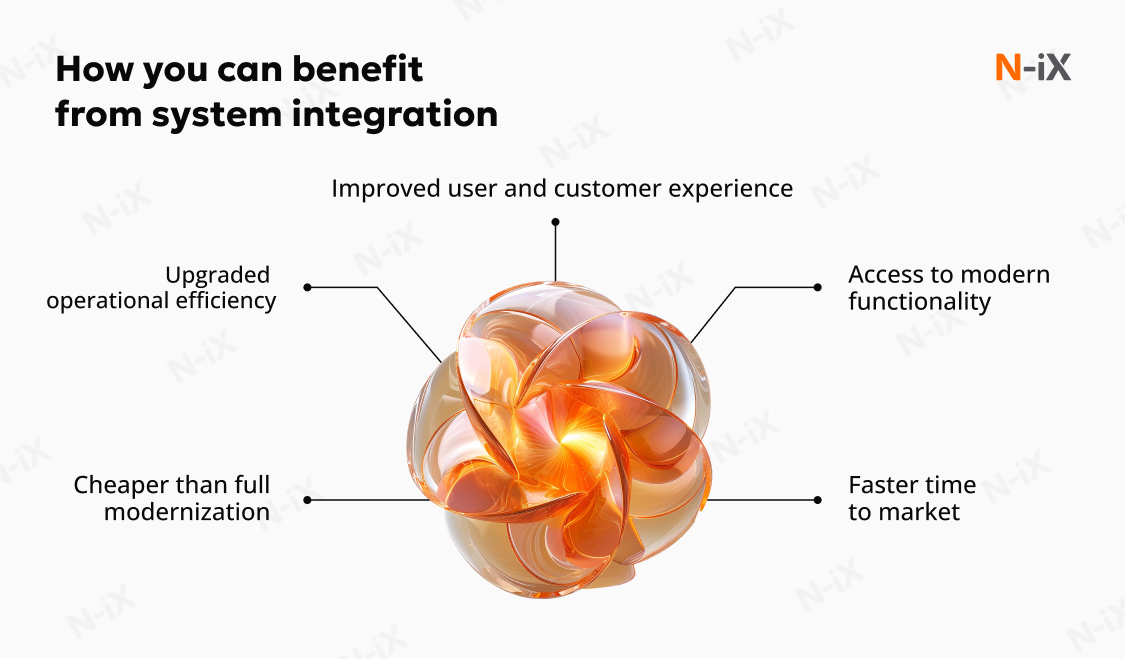
Effective legacy system integration allows organizations to enhance existing infrastructure while introducing modern capabilities in a controlled way. When the connection architecture is designed well, improvements extend beyond performance and directly influence operational outcomes.
- Operational efficiency: Integrated systems eliminate manual data transfers and reduce duplication of work, enabling teams to access accurate information faster and execute processes with fewer delays;
- Cost savings vs full modernization: Integration preserves the value of existing investments, avoiding the immediate expense, disruption, and risk associated with replacing core business applications;
- Access to modern functionality: Organizations can introduce cloud services, automation, analytics, API-driven workflows, and legacy system AI integration while continuing to rely on proven legacy platforms;
- Improved user and customer experience: Unified data and connected workflows create more consistent interactions, faster service delivery, and fewer system-related friction points;
- Faster time to market: Extending current systems instead of rebuilding enables quicker deployment of new capabilities, supporting faster innovation.
Integration vs modernization
When an organization develops needs that its current system doesn’t meet, integration is often the lower-risk, faster option. It preserves proven business logic, avoids major disruption, and enables organizations to introduce new capabilities incrementally. Modernization requires larger investment, longer timelines, and careful change management, but it delivers stronger long-term scalability, maintainability, and performance.
Postponing modernization indefinitely introduces structural risks. Technical debt accumulates, maintenance costs rise, and security exposure increases as unsupported components age. Integration layers may secure the data exchange between systems, but they cannot eliminate vulnerabilities within the legacy application itself. As threat actors continue to evolve their techniques, any unpatched component becomes a predictable entry point.
Read more: Technical debt reduction strategies: Making launchpads for growth
Additionally, many legacy platforms were not designed for modern identity management, encryption standards, or granular access controls. Even when external tools introduce authentication or monitoring, internal processes and data handling may still operate under weaker security assumptions.
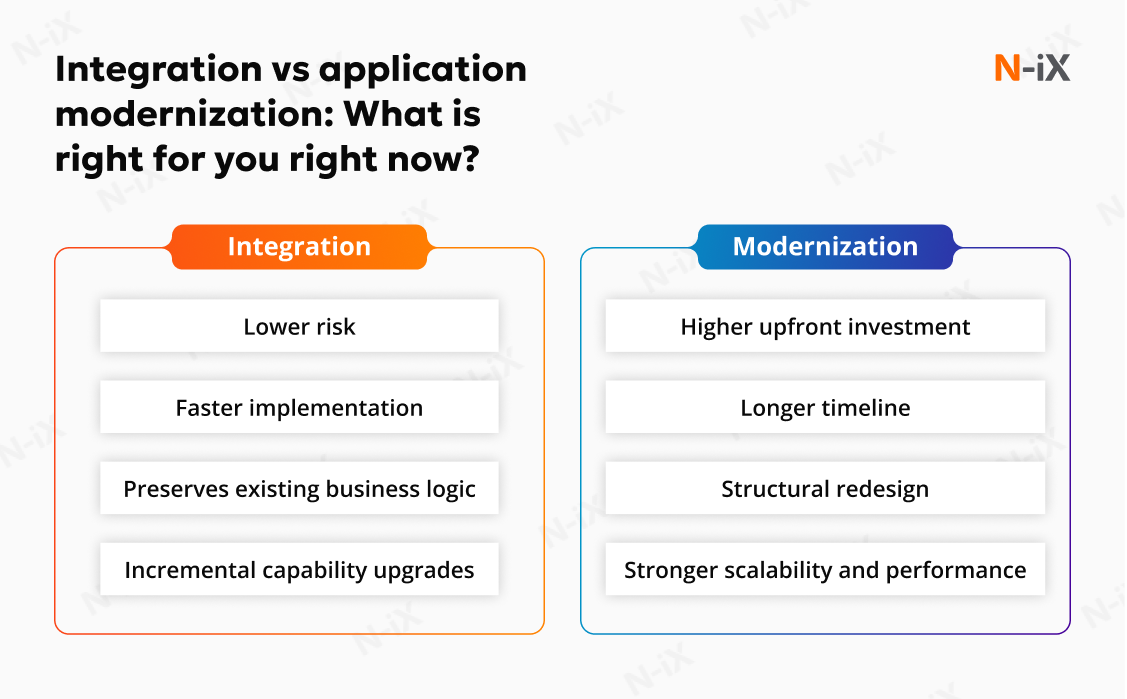
Over time, integration alone can become insufficient, as legacy platforms limit innovation, complicate future upgrades, and create dependencies that make eventual transformation more complex and expensive. N-iX’s experienced engineers and consultants guide you through the application modernization process painlessly.
Legacy system integration challenges
Integrating legacy environments into modern architectures is rarely a purely technical task. Even well-planned initiatives must account for structural constraints that were introduced when these systems were originally designed for stability rather than interoperability. These are the most common challenges of legacy integration:
Technical complexity and limited documentation
Many legacy platforms have evolved through years of incremental changes, custom configurations, and undocumented dependencies. What appears to be a straightforward project can quickly face legacy system integration challenges once hidden interfaces, tightly coupled processes, or outdated codebases are discovered. Without reliable documentation, teams often rely on reverse engineering or the hands-on knowledge of senior engineers, which increases risk and the project timeline.
To overcome this issue, N-iX starts integration projects with a structured technical discovery phase. This includes codebase analysis, dependency mapping, interface identification, and runtime behavior assessment. Teams isolate integration surfaces and define clear system boundaries. Where documentation is missing, automated analysis tools, Gen AI, and targeted reverse engineering are used to rebuild an accurate architectural view.
Learn how generative AI is transforming application modernization
Data silos and incompatible formats
Legacy applications frequently store data in proprietary or outdated formats that were never intended for real-time exchange. As a result, integration requires significant transformation, mapping, and validation to ensure data consistency across systems. Without careful design, organizations risk creating fragmented datasets that undermine analytics and decision-making.
N-iX approaches data integration as a first-class architectural concern rather than a by-product of system connectivity. Data flows are designed explicitly, with clear ownership, transformation rules, and validation checkpoints. This may include tech consultants setting up data governance within the organization.
Security and compliance risks
Older systems were not built to meet current security standards or regulatory requirements. Integrating them into broader digital ecosystems can expose sensitive data through additional connection points, requiring compensating controls such as encryption, access governance, and monitoring to maintain compliance.
N-iX builds security into the way systems are connected from the very beginning, so sensitive data is protected automatically every time systems exchange information. Instead of exposing older systems directly, access is strictly controlled and monitored, making it easier for organizations to meet regulatory requirements and clearly see who accessed what data and why.
Performance and scalability limitations
Legacy infrastructure often struggles to support modern workloads, real-time processing, or high transaction volumes. Integration may introduce latency or throughput bottlenecks that affect downstream applications, particularly when the original system cannot scale without updating hardware.
Rather than forcing legacy systems to behave like cloud-native platforms, N-iX designs integration patterns that respect their operational limits. Asynchronous communication, buffering, and workload isolation are used to protect core systems while enabling modern applications to scale independently.
Approaches to legacy system integration
Organizations can integrate legacy systems in several ways, each suited to different types of solutions, business goals, risk profiles, and levels of technical complexity. Which of the following solutions engineers are going to implement depends on how information needs to move:
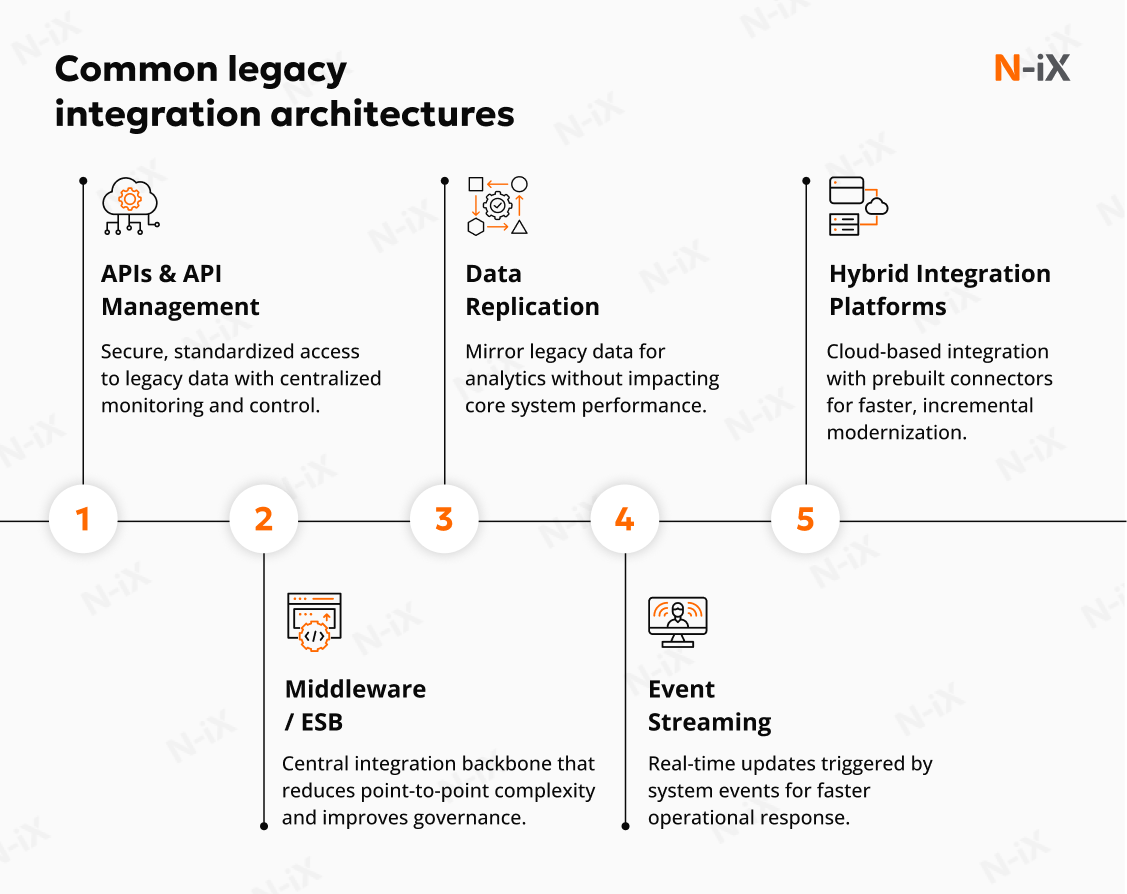
APIs and API management
Rather than allowing every new application to dig into the complicated inner workings of an old database, an API provides a standardized, secure way for modern software to request specific information. This approach is highly effective for businesses looking to build mobile apps or web portals that need to pull data from a core legacy system. When paired with robust API management, leadership gains a centralized dashboard to monitor who is accessing data, ensure security protocols are met, and even monetize data assets if desired.
Middleware and ESB
For organizations operating large, highly interconnected system environments, an Enterprise Service Bus (ESB) provides a centralized integration backbone that standardizes how applications communicate. Instead of managing numerous direct, point-to-point connections, all interactions are routed through a shared integration layer, reducing architectural complexity and improving control. Although an ESB typically requires a higher upfront investment in infrastructure and governance, it offers a stable, predictable foundation for enterprise-scale operations where reliability, consistency, and advanced message orchestration are essential.
Read more: Legacy software modernization: How to part with legacy systems?
Data replication
Rather than placing additional load on systems that are already critical to daily operations, data is mirrored into a separate environment designed for analysis. This approach is commonly used to support business intelligence, reporting, and advanced analytics. Teams gain broader access to insights without compromising the performance, stability, or reliability of the underlying legacy platform.
Event streaming
Instead of relying on one system to request information from another, this integration approach makes the legacy platform announce events, such as a completed transaction, as they occur. These events are distributed through a messaging layer to any connected systems that require the information.
This approach is particularly effective in environments like logistics, fraud detection, and customer service, where even short delays can translate into operational or financial impact. Enabling systems to respond to changes in near real time provides responsiveness typically associated with modern digital systems, while continuing to operate on long-established core software
Hybrid integration platforms (iPaaS)
As organizations shift more workloads to the cloud while continuing to operate business-critical systems on-premises, hybrid integration platforms or Integration Platform as a Service (iPaaS) enable this transition. These platforms operate in the cloud but maintain secure connectivity to internal systems, allowing data and processes to move across environments without forcing immediate replacement of existing infrastructure.
The value of iPaaS lies primarily in speed and adaptability. Prebuilt connectors and standardized integration patterns reduce the effort required to connect new applications, often shortening timelines from months to weeks. This makes iPaaS well-suited for organizations that want to modernize incrementally, balancing the reliability of legacy systems with the flexibility of cloud-native services, while maintaining governance and operational continuity.
Legacy system integration best practices
Legacy system integration services delivery succeeds when it is guided by structure: assessment, deliberate architecture design, disciplined data practices, and rigorous testing reduce risk and prevent new technical debt from emerging. The following best practices ensure integration strengthens long-term modernization instead of introducing hidden vulnerabilities:
Comprehensive technology assessment
Effective integration starts with understanding how the legacy system actually behaves today and what needs to be integrated. Technology assessment services help organizations understand whether their existing systems and infrastructure are ready for integration or modernization by evaluating scalability, security, performance, and architectural constraints in a structured way. This often includes mapping current systems, because you cannot reliably integrate systems you do not clearly understand. Mapping ensures that hidden interfaces or constraints are surfaced before integration work begins.
The anti-corruption layer (ACL)
An anti-corruption layer is the industry standard of legacy system integration best practices. It acts as a protective buffer between legacy systems and modern applications. It translates outdated structures into a clean, consistent format that new systems can rely on. The key benefit is containment. Legacy complexity stays isolated, modern systems remain stable, and future changes become easier to manage. This approach significantly lowers long-term risk.
Data management
Legacy data is often inconsistent and difficult to reuse safely. Strong data practices focus on keeping systems aligned without overloading the legacy platform. Synchronizing changes, using read-only copies for reporting, and validating data before reuse help protect performance and data quality. These steps reduce operational errors and improve trust in downstream systems.
Testing
Testing ensures integrations respect existing business behavior while preventing surprises. Capturing current system behavior and clearly defining data expectations across systems reduces the risk of silent failures. For leadership, this translates into predictability, stability, and fewer production incidents over time.
Explore: Top 15 application modernization companies helping businesses evolve
System integration with N-iX
N-iX’s legacy system integration services are a structured modernization effort. Our engineers start with technical discovery and system mapping to uncover real dependencies, data flows, and architectural constraints before designing integration patterns that preserve business continuity. N-iX applies controlled architecture layers, secure connectivity models, and scalable integration approaches. This ensures legacy environments remain stable while enabling cloud adoption, automation, analytics, and incremental modernization without disrupting critical operations.
N-iX brings broad engineering expertise across cloud architecture, data engineering, cybersecurity, DevOps, and application modernization, with over 2,400 engineers and more than 23 years of experience delivering enterprise-scale projects. With enterprise-scale delivery experience and mature governance practices, we support complex integrations across 22 industries where compliance, performance, and long-term scalability are essential. This cross-domain capability allows N-iX to align integration initiatives with wider digital transformation goals. One of our successful examples of legacy system integration is theimprovement of platform performance by up to 14.5x. This was achieved through the adoption of a modern, cloud-native architecture, effectively reducing technical debt.

Conclusion
Legacy environments are not obstacles by default; they become constraints when integration decisions are made tactically rather than strategically. A structured, engineering-led approach allows organizations to build operational flexibility while maintaining control over risk, compliance, and performance. Done correctly, legacy system integration becomes a controlled evolution of the IT landscape rather than a temporary workaround.
If you are evaluating how to stabilize complex integrations, prepare systems for modernization, or reduce architectural risk, N-iX can help you define a practical roadmap and execute it with enterprise-grade accountability. Engage with our experts to assess your current landscape and identify the next concrete step forward.
FAQ
Is system integration secure?
It can be secure when modern controls such as encryption, authentication, API gateways, and monitoring are implemented. Integration layers often compensate for security gaps in older systems.
Does integration replace modernization?
No. Integration extends the life of legacy systems while enabling new capabilities, and is often used as a step toward gradual modernization.
How long does legacy system integration take?
Timelines vary from weeks for simple integrations to several months for complex, multi-system environments, depending on complexity, data compatibility, and testing requirements.
What skills and tools are required for legacy system integration?
Projects typically require architecture, API, data, and security expertise, supported by tools such as API platforms, middleware, ESBs, data integration tools, and hybrid integration platforms.
Have a question?
Speak to an expert