In 2025, 100% of surveyed businesses experienced revenue-impacting disasters [1], with global annual losses exceeding $2.3T [2]. Cloud outages are no longer rare, and downtime isn’t an exception.
For organizations running workloads in AWS this means treating resilience as an architectural decision and selecting AWS disaster recovery strategies that align with the real business exposure.
But which recovery option provides the right insurance for your specific risk profile? Our guide will help you compare the key resilience models in AWS and provide practical tips for implementing them effectively.
Multi-AZ vs Multi-Region AWS DR strategies
Before selecting a specific recovery method, define your failure domain. Are you protecting against isolated infrastructure issues or an entire Region becoming unavailable?
The first question to consider is how large an event your architecture should be able to withstand.
In AWS development, redundancy operates at two geographic levels: Availability Zones within a single Region, and separate Regions located in different parts of the world. The choice between Multi-AZ and Multi-Region affects network design, data replication patterns, failover automation, and overall operational complexity.
-
Multi-AZ
Availability Zones are physically independent data centers located within the same Region. Deploying workloads across multiple AZs protects you against mundane failures like power outages, hardware crashes, or damaged fiber cables. This AWS DR strategy is the industry standard for daily reliability, since multi-AZ support is built into AWS services and can be enabled without adding cross-Region data transfer costs. However, it leaves your assets vulnerable to major events impacting the entire Region. For instance, if a massive grid failure takes out the whole metropolitan area, you’re still offline.
-
Multi-Region
To mitigate the risk of widespread outages caused by natural disasters or broad service disruptions, you need multi-Region resilience. This practice moves your recovery site to a completely different part of the country or even a different part of the world. This ensures that even if an earthquake or a major regional outage occurs, your business survives because your backup is thousands of miles away from the danger zone. The trade-off for business continuity in this case is higher data transfer costs, infrastructure costs, and architectural complexity.
Most robust architectures combine these approaches: they rely on multi-AZ for everyday reliability while reserving multi-Region replication for the worst-case scenarios.
Many organizations also strengthen resilience during broader cloud transition. As part of our partnership with a large international bank, N-iX implemented cross-environment replication from on-premises systems to AWS. Our team established a cloud-based DR setup aligned with strict regulatory requirements, enabling our client to protect sensitive customer data and prepare for disaster scenarios.
Read the full case study: Robust data protection and disaster recovery in banking with migration to AWS
With your geographic scope defined, let’s explore the four main AWS disaster recovery strategies.
4 key AWS disaster recovery strategies
Not all DR strategies are designed for the same level of resilience. Some prioritize cost efficiency and simplicity. Others aim for near-continuous availability across Regions. The right choice depends on how much downtime and data loss your business can tolerate, and how much complexity you are prepared to manage.
An effective AWS disaster recovery strategies’ comparison starts with two metrics that guide architectural decisions and budget allocation:
- Recovery time objective (RTO) describes how long you can afford to be offline. Higher RTO means longer recovery time.
- Recovery point objective (RPO) describes how much data you can afford to lose, measured as the time between the last consistent backup and the disruption.
Availability targets also matter. For example, 99% uptime over a full year allows approximately 87 hours of downtime. If that same 99% applies only to business hours, the acceptable downtime shrinks significantly, which may require a different recovery architecture.
Each of the four strategies below represents a different tier of resilience. Let’s take a closer look at them.
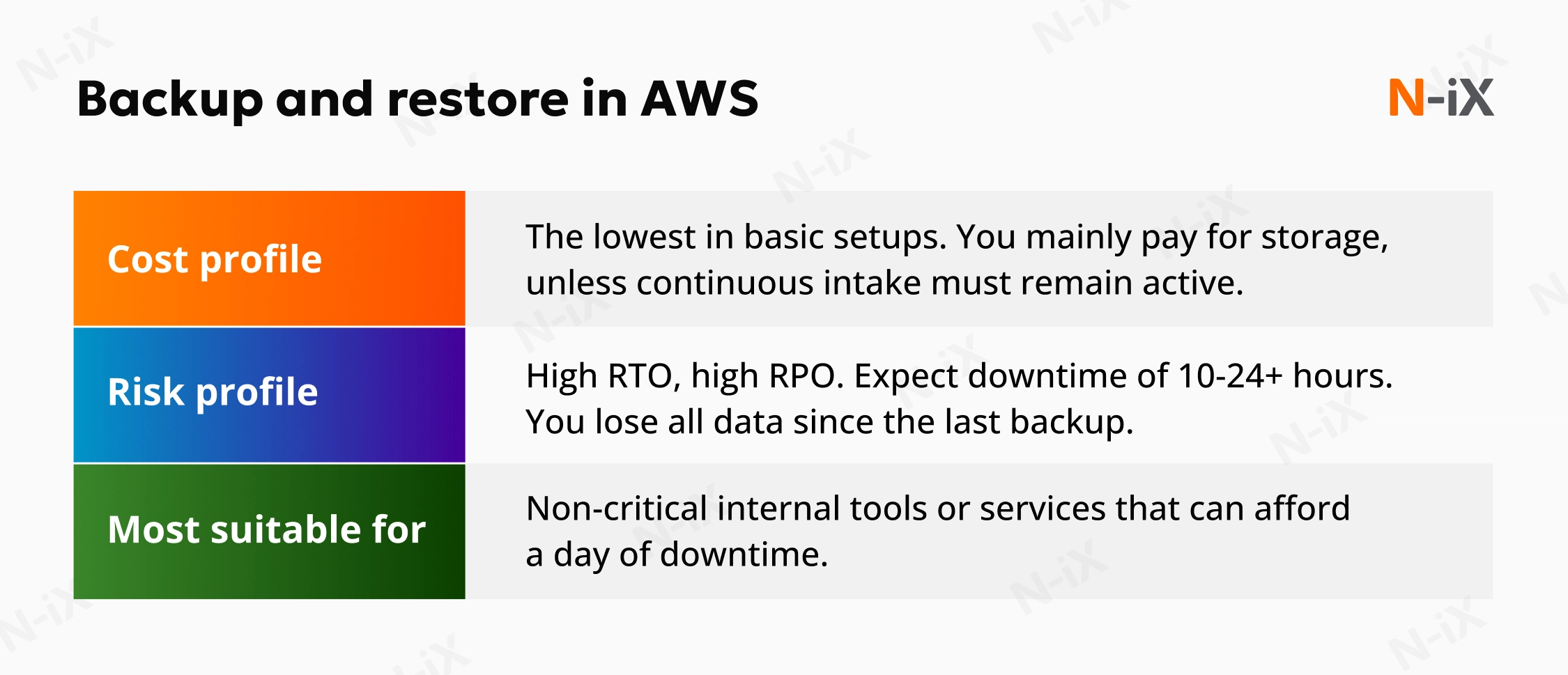
Strategy 1: Backup and restore
This AWS disaster recovery strategy works like a savings account. It’s a safe, reliable, and affordable option to maintain, but withdrawing your assets takes time. In this scenario, your data is regularly backed up and stored in low-cost storage tiers like Amazon S3 or Amazon S3 Glacier. In case something goes wrong, you can restore your systems from backups.
The trade-off is the time it takes to restore your assets. When disaster strikes, you aren’t just flipping a switch. You must retrieve data, provision new servers, and reinstall software to rebuild your environment from the ground up. Consequently, this results in the highest RTO, typically measured in hours or even days.
Our advice: Avoid relying on manual rebuilding. Use Infrastructure as Code tools such as AWS CloudFormation or AWS Cloud Development Kit to automate the rebuilding process. If your team needs to manually reinstall servers after an outage, the expected 24-hour recovery period could easily turn into a week.
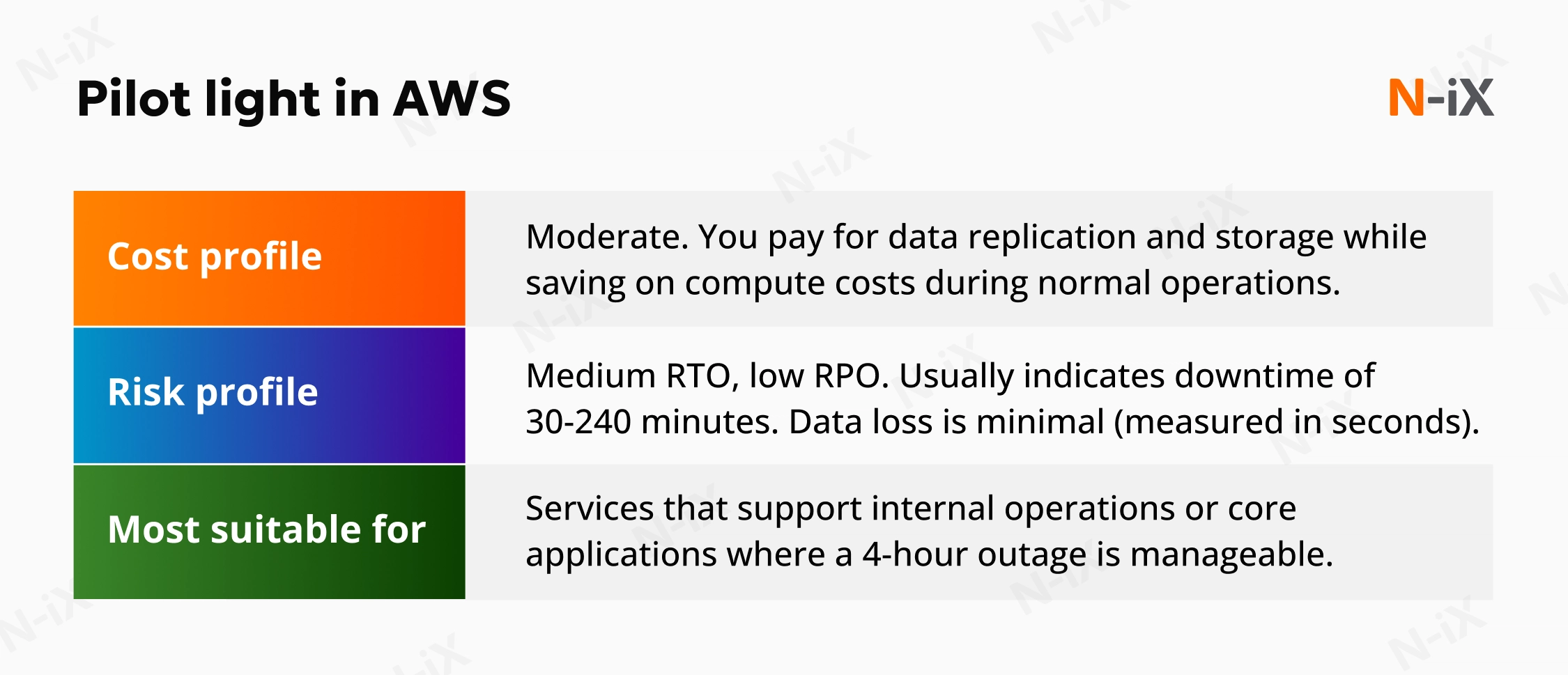
Strategy 2: Pilot light
This approach is one of the AWS disaster recovery strategies that strikes a balance between cost and speed. It gets its name from a gas furnace: a small flame is always burning, ready to ignite the entire system the moment heat is required.
In AWS terms, the “flame” is your data. You continuously replicate your critical databases and object storage from your primary region to your recovery region. While this data is live and up to date, the application layer in the recovery region is not fully running. Your servers, load balancers, and other compute resources are provisioned only when needed. This helps avoid paying for idle capacity while keeping the environment ready for rapid activation.
When a disaster is declared, you deploy the required resources, connect them to the already-replicated data, and scale the environment to handle production traffic. Since the data is already available, you skip the lengthy restore phase of the backup and restore approach. You only wait for the servers to boot and the network to be configured, reducing recovery time from days to hours or even minutes, depending on automation maturity.
N-iX’s tip: The biggest risk with pilot light is configuration drift. Our cloud experts frequently see companies try to activate their recovery environment only to find their backup servers are running software from six months ago. To ensure your standby setup always mirrors production, automate the creation and update of Amazon Machine Images (AMIs). Every time you update production, your recovery images should be updated accordingly.
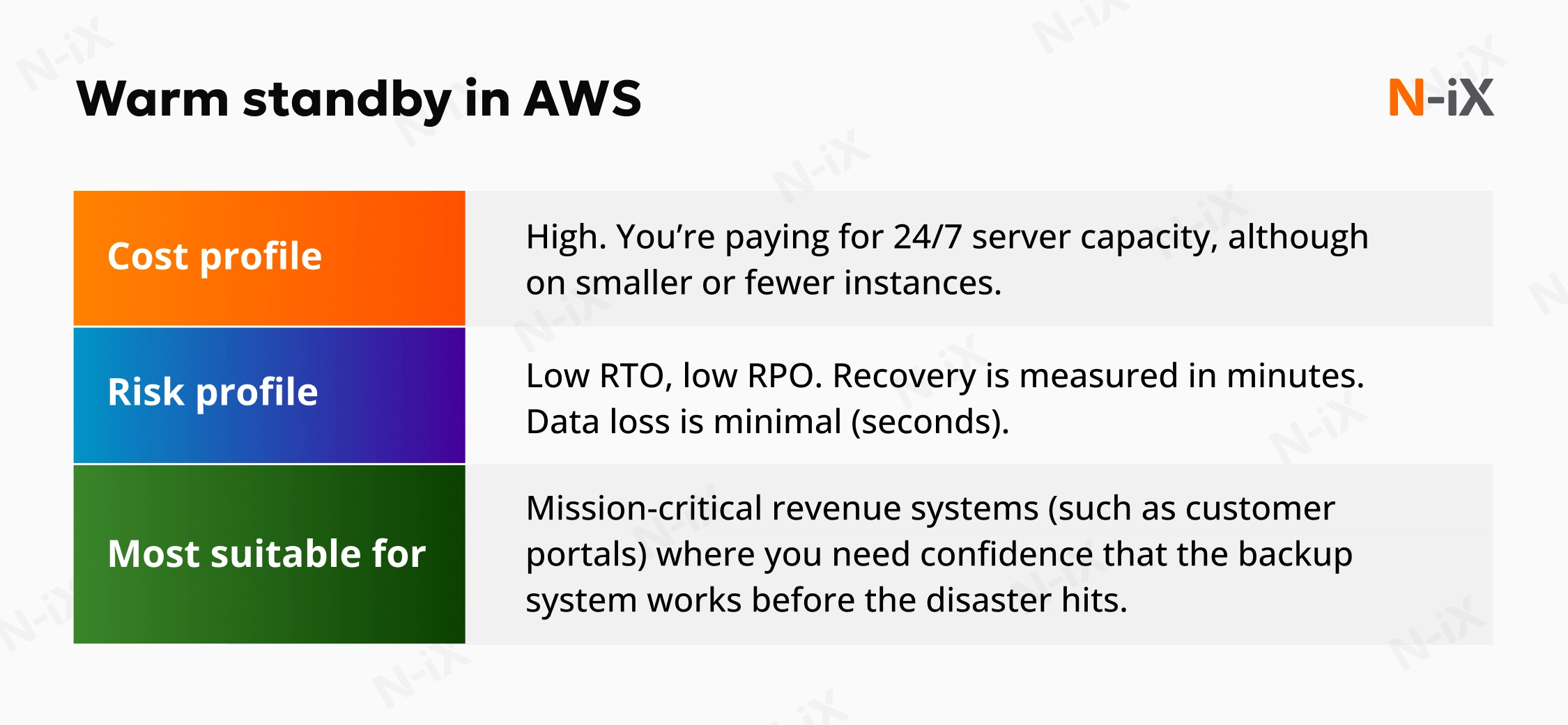
Strategy 3: Warm standby (active/passive)
In this strategy, you maintain a fully functional version of your environment in a secondary region, but it runs on minimum capacity. Your load balancers, application servers, and databases are all online and replicating data in real time. However, instead of running, for example, 50 large production servers, you might run only two small ones to maintain minimal capacity.
Since the secondary environment is always running, you can continuously validate its readiness. Teams often route synthetic user traffic through the standby system to confirm that applications, integrations, and data replication function as expected. When a disaster occurs, there is no boot phase or infrastructure provisioning delay. Instead, you trigger AWS Auto Scaling to increase capacity from the minimal footprint to full production scale. The environment shifts from reduced capacity to full operational load within minutes.
Our experts note: A significant advantage of warm standby is the possibility of continuous testing. With the previous strategies, you only know if your DR plan works during a drill. With warm standby, because the endpoints are live, you can configure automated health checks that log in and perform actions at regular intervals. If your backup site breaks, you’ll learn about it immediately and not during an emergency.
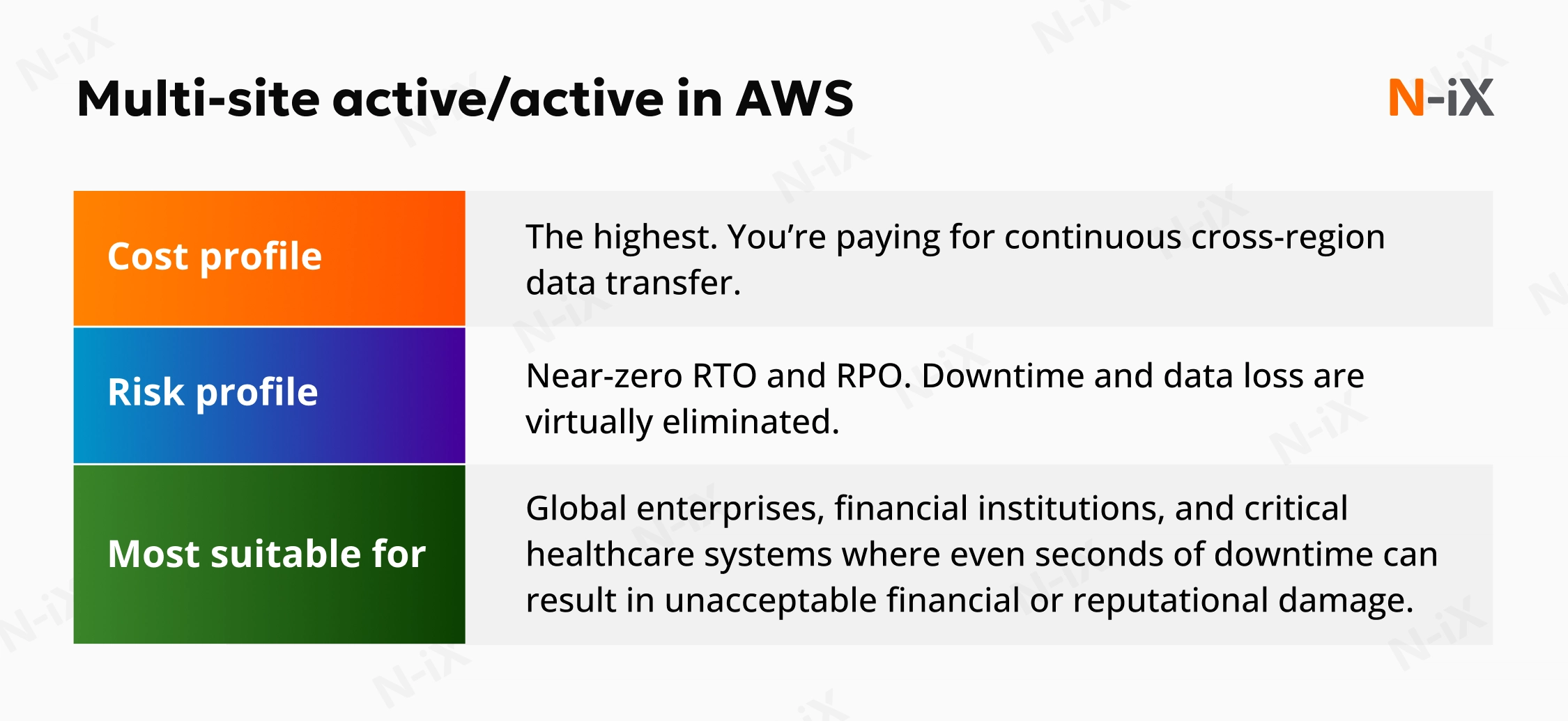
Strategy 4: Multi-site active/active
Among all the AWS disaster recovery strategies, this option offers the maximum level of resilience. This architecture maintains two or more fully operational production environments in different geographic regions simultaneously. The assets in those regions don’t sit idly, nor are they scaled down.
In this setup, your user traffic is distributed across both regions (for example, US East and US West) using services like Amazon Route 53 or AWS Global Accelerator. If an entire region goes offline, the traffic routing service detects the failure and directs all users to the remaining healthy region. Since both sites are already active and scaling to meet demand, there is effectively no recovery time. The failover is seamless, often happening without the user even noticing a disruption.
N-iX’s experts point out: While AWS handles the infrastructure, your application logic must handle data synchronization. Write conflicts represent one common challenge: if two users update the same record in different regions at the same time, which update wins? Implementing this strategy often requires re-architecting your application to mitigate data corruption risks.
Key tips for implementing disaster recovery strategies on AWS
Selecting a recovery approach is a large but not final part of the equation. Implementation comes down to clear priorities, repeatable processes, and proven recovery principles that keep your plan effective as systems evolve. Let’s take a look at the practical tips that help you reduce disruption while staying within budget.
Consider the cost vs speed trade-off
Lower RTO and RPO targets require greater infrastructure duplication, continuous replication, and more advanced automation. As resilience increases, so do operational costs. When evaluating DR strategies in AWS, balance the financial impact of downtime against the ongoing investment required to maintain faster recovery.
Assess your workloads and determine their criticality
Different systems require different levels of resilience. Applying the most advanced setup to every workload often leads to unnecessary costs and operational overhead. For instance, a marketing website doesn’t justify the same architecture as a payment platform or a production control system.
When selecting among AWS disaster recovery strategies, align recovery patterns with business impact. Our experts recommend assessing your cloud workloads and categorizing them into tiers based on criticality:
- Tier 1: Revenue-generating and customer-facing applications, such as ecommerce platforms, payment systems, trading applications, and core production systems. The most suitable recovery strategies typically include warm standby or multi-site active/active.
- Tier 2: Internal operations and business support systems, such as ERP platforms, CRM systems, analytics environments, and internal collaboration tools. The most appropriate strategy for these is often a pilot light.
- Tier 3: Archives and non-critical workloads, such as historical data stores, development environments, and marketing content repositories. Backup and restore is typically sufficient for these workloads.
In addition to business criticality, identify control plane dependencies for each workload. Authentication services, DNS, networking, orchestration, and CI/CD pipelines often act as hidden single points of failure. If the control plane is unavailable, recovery may stall even if application data is intact.
Then, focus on defining the following metrics for each application:
- RTO: Maximum acceptable downtime.
- RPO: Maximum acceptable data loss.
- Service level indicator (SLI): The metric used to measure service performance, such as latency or availability.
- Service level objective (SLO): The target value for a given SLI.
- Service level agreement (SLA): The contractual commitment tied to service performance.
Conduct regular testing
You only know whether your disaster recovery plan works as intended when you test it. Regular failover drills confirm that your RTO targets are achievable in practice. Testing also exposes configuration drift as environments evolve. Infrastructure changes, dependencies are updated, and new releases are deployed. Without scheduled simulations, your standby setup may no longer match production when you actually need it.
Automate the recovery process
A recovery process that depends on manual intervention increases risk during an outage. In high-pressure situations, delays and human error can undermine even well-designed architectures. Automate infrastructure provisioning and failover workflows to ensure recovery is executed consistently and quickly. Use tools such as AWS CloudFormation or Terraform to define and rebuild environments as code and reduce uncertainty.
Also, site reliability engineering (SRE) helps turn automation into an operational standard that you can rely on during real failures. SRE practices encourage you to codify recovery paths, test them regularly, and tie automation directly to reliability targets such as RTO, RPO, and service-level objectives.
Partner with specialized cloud consultants
AWS provides powerful tools for DR, such as Route 53, Aurora Global Database, and Elastic Disaster Recovery. However, connecting these services requires a clear understanding of failure domains, replication models, automation, and cost trade-offs. Evaluating AWS disaster recovery options often involves nuanced design decisions that call for specialized expertise.
Outsourcing DR to an experienced cloud consulting partner like N-iX enables you to align disaster recovery architecture with actual business impact. We assess your risk exposure and regulatory constraints to design a strategy that protects revenue, preserves customer trust, and keeps operational disruption within defined limits.
Key takeaways
- The four AWS disaster recovery strategies are backup and restore, pilot light, warm standby, and multi-site active/active.
- Multi-AZ and Multi-Region solve different problems. Multi-AZ protects against localized failures, while Multi-Region prepares you for large-scale regional outages.
- RTO and RPO determine your recovery posture, with lower tolerance for downtime and data loss requiring greater architectural and financial investment.
- Not all workloads need the same level of resilience. Categorizing systems by business criticality prevents overspending on non-essential services.
Why choose N-iX for implementing an AWS DR strategy?
As an AWS Premier Tier Services Partner with over 180 certified AWS experts on board, N-iX implements recovery plans aligned with your RTO, RPO, and compliance requirements. With 23 years of engineering experience, we assess your current AWS architecture, identify risk exposure, and design resilient multi-AZ or multi-Region setups tailored to your business priorities. Our processes align with leading cybersecurity standards, including ISO 27001, ISO/IEC 27701, PCI DSS, and CyberGRX, to support secure and controlled operations. This structured approach makes N-iX a reliable partner for strengthening your operational continuity and regulatory readiness.
References
- The State of Resilience 2025—Cockroach Labs
- 2025 Global Assessment Report on Disaster Risk Reduction—United Nations Office for Disaster Risk Reduction
Have a question?
Speak to an expert